Anyone who has worked on an embedded project has inevitably faced this question: "What's the best way to verify that data was transmitted correctly?" It often starts with a simple summation (Checksum), then you realize the error detection isn't sufficient and switch to CRC, only to later find yourself confronted with security requirements you hadn't considered.
Checksum, CRC (Cyclic Redundancy Check), and cryptographic hashes (SHA-256, MD5) — all three share the common goal of data integrity verification, but their mathematical structure, security strength, and appropriate use cases are entirely different. Choosing the wrong one either wastes performance or, worse, introduces a security vulnerability.
Checksum, CRC, Hash — The Essence of Three Approaches
The fastest way to understand these three algorithms is to view them through the lens of: "How easily can an attacker bypass detection if they tamper with the data?"
Simple Checksum
This is the most basic form of integrity verification. It simply sums all bytes of the data and appends the result to the end of the frame; the receiver performs the same calculation and compares the values.
The calculation is simple and fast, but because simple summation-based checksums have a linear structure, they cannot detect permutation errors (swapped byte order) or bit changes that cancel each other out (+x / −x). For example, 0x01 0x02 and 0x02 0x01 produce the same sum. The IPv4 Header Checksum is a representative example of this approach — more precisely, it uses a 16-bit one's complement summation, yet still shares the same fundamental limitation of failing to detect reordering or cancellation errors. This is precisely why it is used in combination with upper-layer (TCP/UDP) checksums.
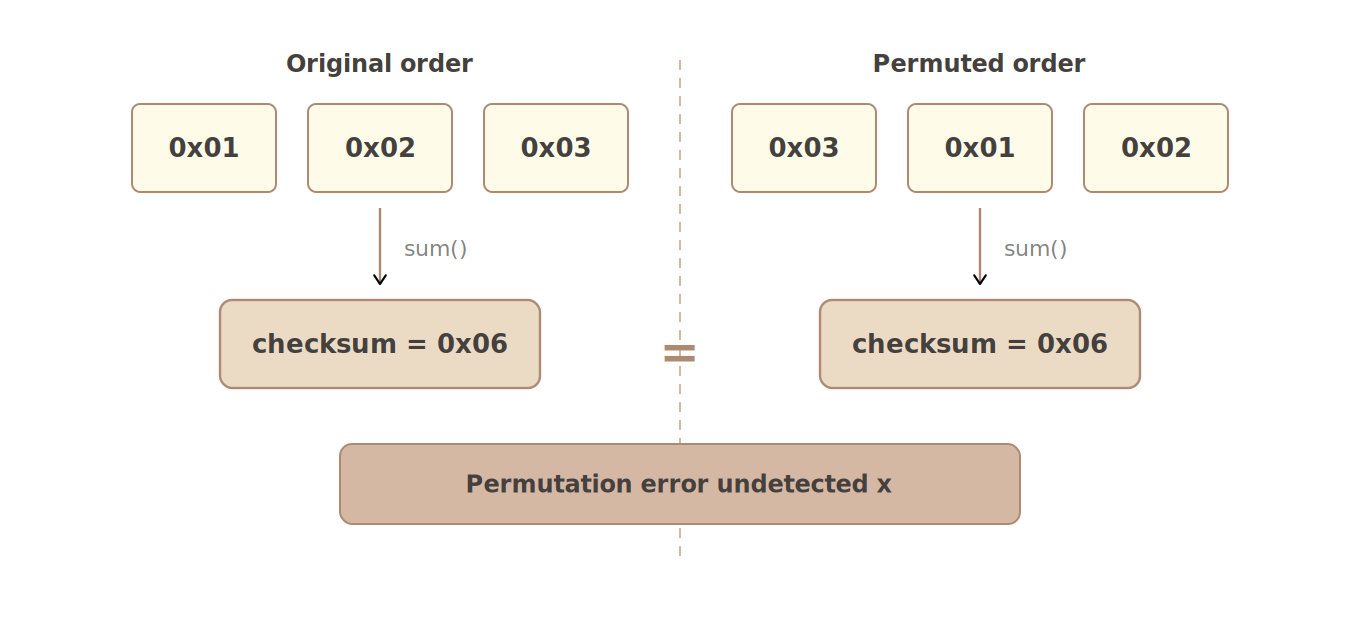
A simple Checksum cannot detect byte-reordering errors. Two completely different data sequences produce the same checksum value.
CRC (Cyclic Redundancy Check)
CRC adopts polynomial division as its mathematical foundation to overcome the limitations of simple summation. It represents data as a binary polynomial and uses the remainder from dividing by a predetermined generator polynomial as the checksum.
Thanks to this mathematical structure, CRC can detect complex error patterns with high probability — such as burst errors and data reordering — that simple checksums cannot catch. Additionally, many CRC generator polynomials include the (x+1) factor, meaning they can detect all odd numbers of bit errors (CRC-32, CRC-16/IBM, etc.). Since CRC-32's generator polynomial has degree 32, it detects 100% of burst errors up to 32 bits, with detection becoming probabilistic for longer burst errors.
CRC is used in various industry standards including Ethernet (CRC-32/ISO-HDLC), MODBUS RTU (CRC-16/MODBUS), CAN Bus (CRC-15/CAN), and file formats like ZIP and PNG. However, there is an important constraint: CRC is a tool for detecting accidental errors, not a security tool for preventing intentional tampering. A malicious attacker can reverse-engineer a way to alter data while maintaining the same CRC value.
Cryptographic Hash Function
Cryptographic hashes like SHA-256, SHA-3, and MD5 are designed to go beyond simple error detection and defend against intentional data manipulation. SHA-256, defined by NIST FIPS 180-4, guarantees the Avalanche Effect — a single bit change in the input causes more than half of the output hash to change completely.
Cryptographic hashes have three core security properties. First, Preimage Resistance — recovering the original data from a hash value is computationally infeasible. Second, Second Preimage Resistance — finding a different input that produces the same hash value is computationally infeasible. Third, Collision Resistance — finding any two inputs that share the same hash value within practical time is computationally infeasible.
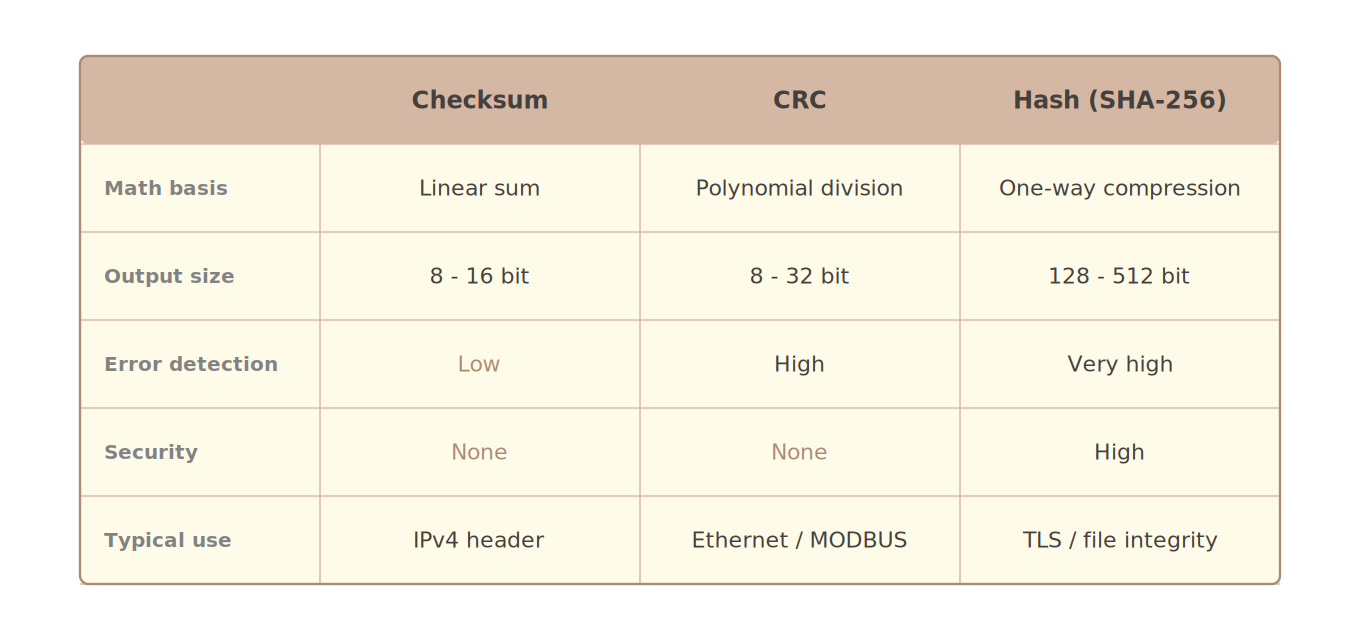
Key characteristics comparison of the three algorithms. CRC is appropriate for communication protocols without security requirements; cryptographic hashes are appropriate for digital signatures and file authentication.
MD5 Is No Longer Secure
When discussing cryptographic hashes, the security lifespan of MD5 must be addressed. MD5 has been used for file integrity verification and digital signatures since it was defined in RFC 1321 in 1992. However, a 2004 paper by Wang et al. demonstrated that practical collision attacks against MD5 were possible, and as attack techniques continued to advance, modern chosen-prefix collision attacks made it possible to generate MD5 collisions within practical time even on ordinary computers.
This was formally documented in the 2011 IETF RFC 6151, which states that MD5 is no longer acceptable for applications requiring collision resistance, such as digital signatures.
There is only one use case where MD5 remains acceptable: detecting simple transmission errors in environments free from malicious tampering — for example, file transfer checks between internal systems. However, adopting MD5 in new system designs is not recommended.
The current choices are SHA-256 (SHA-2 family) or SHA-3. SHA-256 produces a 256-bit output, has no known collisions to date, and underpins modern security infrastructure including TLS, Git, and Docker image signing.
Decision Criteria in Practice
Here is a summary of when to use each algorithm.
Use Simple Checksum when: computing resources are severely constrained (ultra-small microcontrollers), integrity verification is already handled by a separate upper layer, or speed is overwhelmingly more important than error detection.
Use CRC when: the purpose is accidental error detection in environments without security threats — such as industrial communication protocols (MODBUS, CAN Bus), file format error detection (ZIP, PNG), or memory integrity checks in embedded systems.
Use a Cryptographic Hash when: any situation requires defending against data manipulation by external attackers — including software distribution file integrity verification, digital signatures, password hashing (combined with bcrypt/Argon2), and TLS certificates.
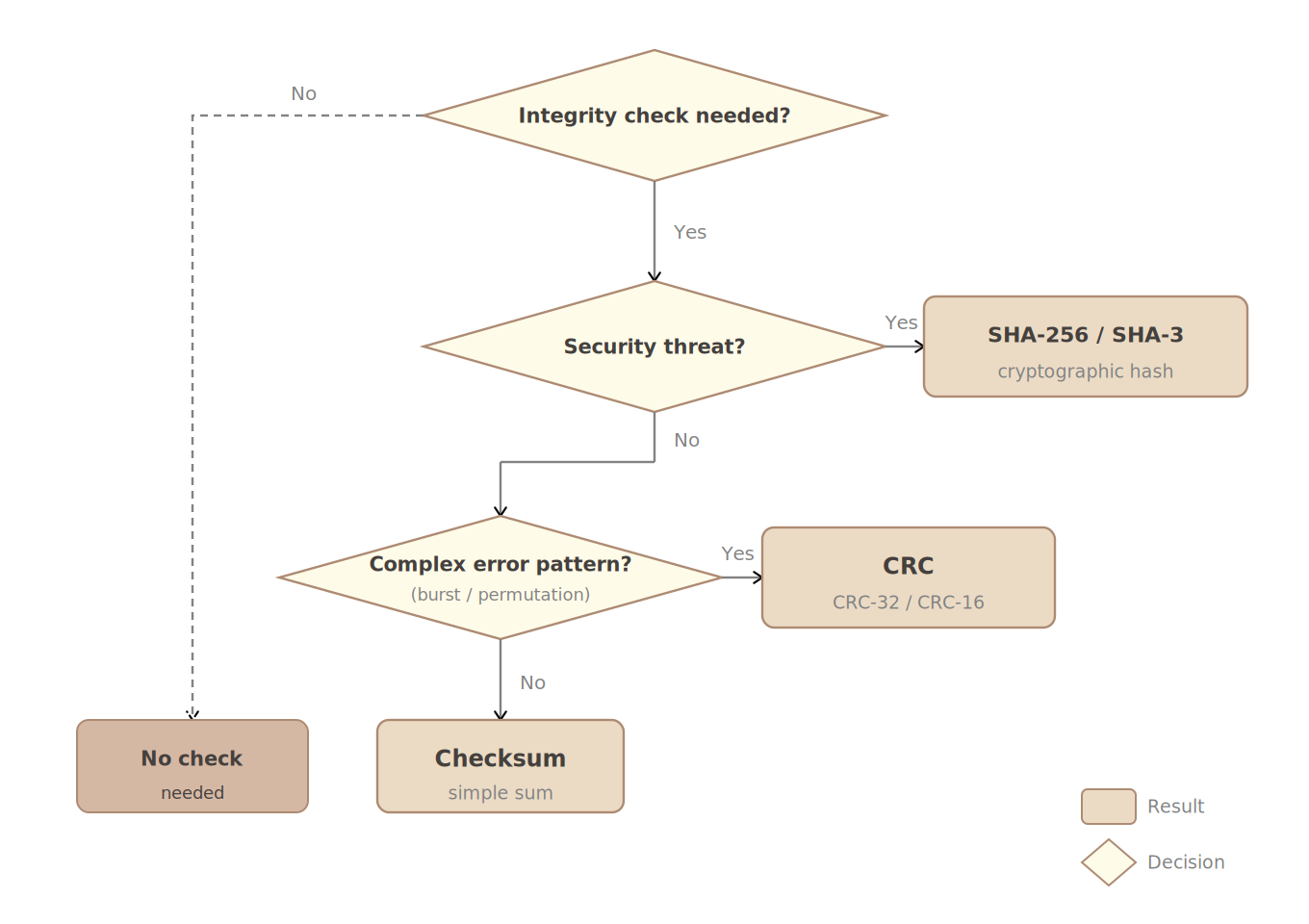
A decision tree for algorithm selection. The presence or absence of a security threat is the most critical branching criterion.
Calculating and Verifying CRC Values
When implementing or debugging CRC-based communication protocols, you need a tool to quickly verify the computed result of a specific algorithm. CRC Tool supports over 100 algorithms from CRC-8 to CRC-64, and lets you instantly switch byte order to match protocols like MODBUS RTU that require little-endian output. With options such as HEX input, byte-separated output, and endianness settings that come up frequently in practice, it is especially useful during the verification phase of CRC implementations.
Latest Trends: SHA-3 and the Future of Hashing
The SHA-2 family (SHA-256, SHA-512) is currently considered secure, but NIST additionally standardized SHA-3 (based on the Keccak algorithm) in 2015 (Keccak was selected through the SHA-3 competition in 2012). SHA-3 has a completely different internal structure from SHA-2, providing strategic independence — even if a theoretical weakness were discovered in SHA-2, SHA-3 would remain unaffected.
For password storage specifically, using SHA-256 alone is insufficient. Because it is vulnerable to GPU-based parallel attacks, it must be used alongside intentionally compute-intensive key derivation functions (KDFs) such as bcrypt, Argon2, or scrypt.
Post-Quantum Cryptography is actively being discussed in preparation for advances in quantum computing. For hash functions, the quantum Grover's algorithm roughly halves effective security strength. For example, SHA-256 provides 128-bit security against classical computers, but drops to approximately 64-bit under Grover's algorithm. The proposed countermeasure is to double the output length (SHA-512, SHA3-512) — SHA-512 maintains 128-bit security strength even in a quantum environment.
CRC vs MD5: Why Can't CRC Be Used for Security?
In practice, the two are sometimes conflated or people wonder, "Isn't CRC good enough?" Understanding the fundamental difference between the two algorithms answers this question definitively.
CRC was never designed with security in mind. The output of CRC-32 is only 32 bits (approximately 4.3 billion possible values), and because the generator polynomial and algorithm are public, an attacker can mathematically reverse-engineer a way to manipulate data while preserving the target CRC value. This is called CRC forgery — meaning a maliciously modified file can have the same CRC value as the original.
MD5, on the other hand, has a 128-bit output and a one-way compression structure designed to make inversion computationally infeasible. Of course, as explained above, MD5 is also vulnerable to collision attacks, so SHA-256 should be used for security purposes.
In summary, CRC is a tool for catching accidental errors such as channel noise or physical damage, while cryptographic hashes are tools for stopping attackers with intent. The two serve fundamentally different purposes, so they should be understood as complementary rather than interchangeable.
Conclusion: Purpose Determines the Tool
Using SHA-256 for error detection in an embedded communication frame is an excessive waste of resources. Conversely, verifying the integrity of a software distribution file with only CRC is a serious security hole. The key is to first understand the security properties each algorithm guarantees — not just its name — and then choose the one that fits your situation.
If you need a CRC calculation tool or want to verify a CRC implementation, check out CRC Tool. It lets you instantly compare multiple algorithms against the same input, helping you identify the exact algorithm your protocol specification requires.
References
- R. Rivest, "The MD5 Message-Digest Algorithm", RFC 1321, IETF, April 1992.
- S. Turner, L. Chen, "Updated Security Considerations for the MD5 Message-Digest and the HMAC-MD5 Algorithms", RFC 6151, IETF, March 2011 — The document that formally codified MD5's security vulnerabilities and usage restrictions.
- NIST, "Secure Hash Standard (SHS), FIPS 180-4", 2015 — The official standard specification for the SHA-2 family of algorithms including SHA-256 (SHA-224, SHA-256, SHA-384, SHA-512, etc.).
- NIST, "Hash Functions", CSRC — List of NIST-approved hash algorithms and security strength comparison table.
- Ross Williams, "A Painless Guide to CRC Error Detection Algorithms" — An essential reference explaining CRC parameters and operating principles in detail.